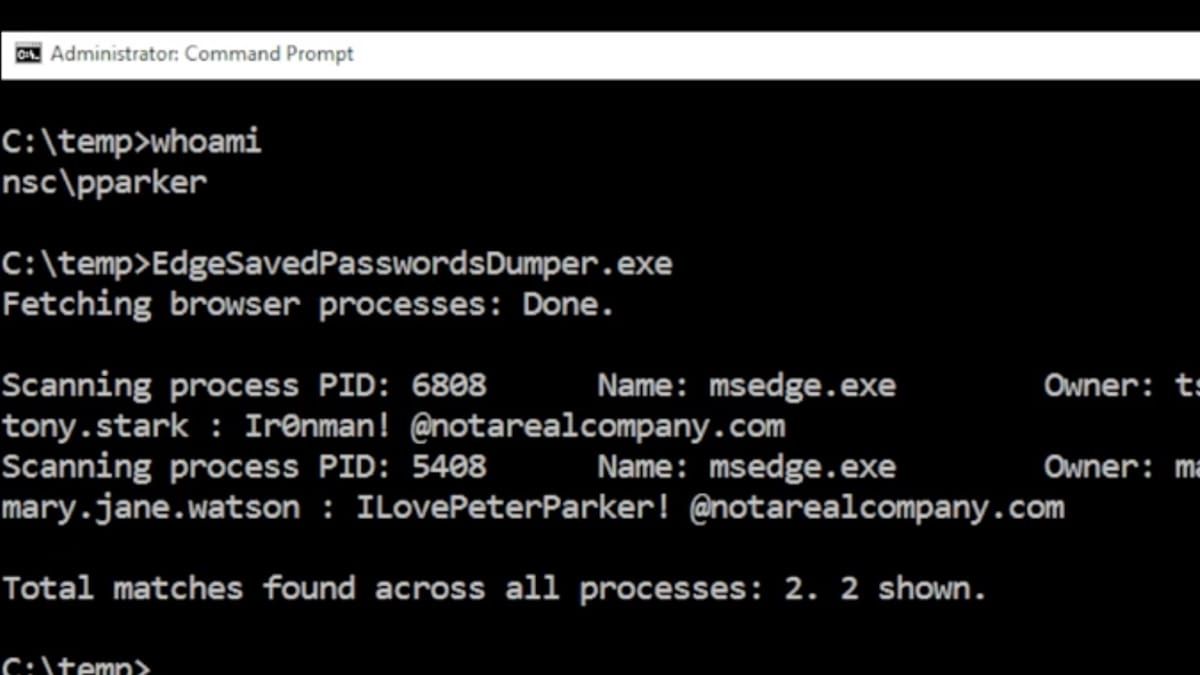
Microsoft Edge holds plaintext passwords in process memory after autofill, a new analysis shows. Any attacker or insider with access to a memory dump can retrieve every password the user ever entered through the browser.
It’s a bypass of two standard enterprise defenses: Windows Hello, Microsoft’s passwordless authentication system, and DPAPI, the Windows Data Protection API that encrypts credentials at rest. Neither applies once a credential is sitting unencrypted in RAM.
Enterprise environments carry the sharpest exposure. IT teams relying on Windows Hello to limit credential risk may not know the browser retains a plaintext copy of every autofilled password in memory. Running a memory dump against the Edge process retrieves the full list. Memory dumps are a standard forensic technique, and they’re a well-known attacker move.
The scope is broad. Every password a user ever entered through Edge’s autofill remains recoverable from process memory, the analysis found. Enterprise security teams will need to decide whether they can trust Edge as a managed password manager.